Security is leadership work
Security teams handle technical tasks. Leaders handle priorities, decisions, and accountability. When something goes wrong, it is rarely because nobody knew how to fix it. It is because the organization did not prioritize the right fixes, did not fund the basics, or did not enforce ownership.
Many executive teams want a simple answer. Are we safe. The honest answer is a range, not a single yes or no. Readiness is not one product or one dashboard. It is the strength of your controls, the clarity of your operating model, and the quality of your response discipline.
Non-technical executives do not need deep technical language. They need a way to understand exposure, assign owners, and drive action without getting lost in tool names and engineering detail.
What security readiness means in plain language
You are security ready when three things are true.
- Prevention. Common attacks fail because the basics are strong.
- Detection. When something slips through, you see it quickly.
- Recovery. If systems go down, you restore operations without prolonged business damage.
If any one of these is weak, risk rises fast. Prevention without detection creates blind spots. Detection without recovery creates panic. Recovery without prevention becomes expensive and frequent. Executives should think of readiness as a balanced operating condition, not a technical score.
The executive risk map
Non-technical leaders need a short risk map that stays stable over time. You do not need to track every vulnerability. You need to track the categories that create business impact, expose customer data, interrupt operations, or increase regulatory and vendor exposure.

1. Identity and access
Most breaches start with access. Compromised credentials, over-privileged accounts, shared logins, and weak offboarding all create avoidable exposure. Require visibility into how access is granted, reviewed, and removed.
- Do all critical systems require MFA.
- Do privileged accounts have stronger controls than normal users.
- Do we remove access within 24 hours of termination or role change.
2. Data exposure
Data risk is about where sensitive data lives, who can reach it, and how it moves. Demand a clear map of regulated data and customer data, plus the controls that protect it.
- Where is regulated or sensitive data concentrated.
- Which teams and vendors have access.
- Do we log access and detect unusual activity.
3. Vendor and SaaS exposure
Vendors expand your attack surface. Every integration and admin account is a potential entry point. Require a vendor register with risk tiering, contract controls, and periodic reviews.
- Do we know which vendors have access to production systems or sensitive data.
- Do contracts include security requirements and incident notification timelines.
- Do we review vendor access quarterly and remove what is not needed.
4. Resilience and recovery
Recovery is where executives feel the impact. Downtime, missed revenue, service disruption, and operational confusion all show up fast. The strongest signal of readiness is tested recovery, not a document sitting on a shared drive.
- Do we have documented recovery objectives for critical systems.
- Do we run quarterly restore tests for backups.
- Can we operate manually if a core system is down.
5. Operational discipline
Security depends on the operating model. Patch cadence, change control, configuration management, asset inventory, and monitoring all shape exposure. You do not need tool details. You need health indicators and trend.
- Do we know what systems we run and who owns them.
- Do we patch critical issues within an agreed window.
- Do we monitor and investigate alerts consistently.
6. Compliance and audit risk
Compliance is not security, but it often reveals where controls are weak. Treat audits as risk discovery. Require action plans, named owners, and timelines for remediation.
- Do we track audit findings to closure.
- Do we test controls, not only document them.
- Do we measure reduction in repeat findings.
Turn risk into a decision matrix
Use a consistent method to decide what to fund, what to pause, and what to escalate. A simple likelihood versus impact view keeps leadership discussion grounded in business exposure instead of technical noise. Then attach clear actions to each quadrant.
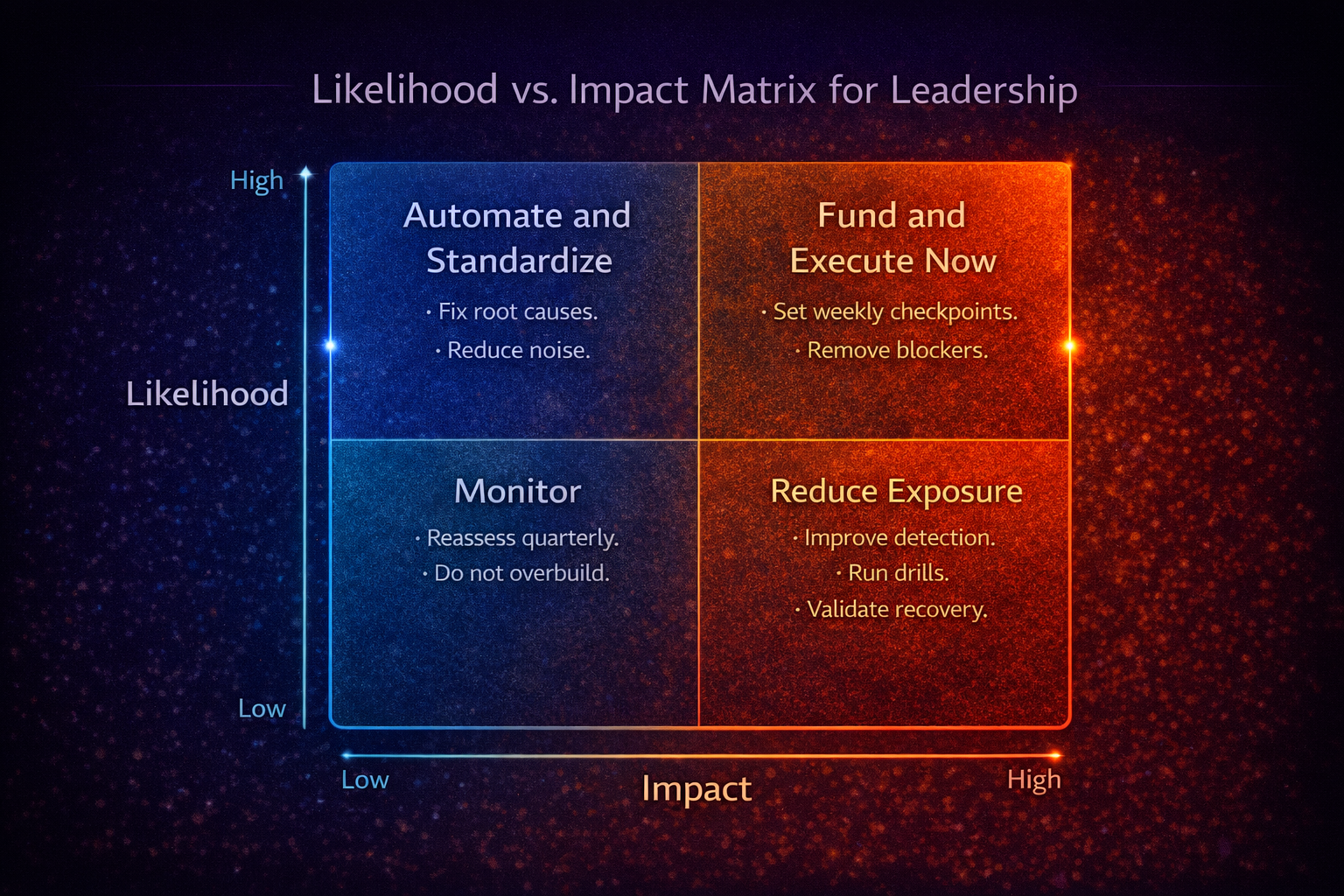
How to use the matrix in leadership meetings
- High impact, high likelihood. Fund and execute now. Set weekly checkpoints. Remove blockers.
- High impact, low likelihood. Reduce exposure and improve detection. Run drills. Validate recovery.
- Low impact, high likelihood. Automate and standardize. Fix root causes. Reduce repeat noise.
- Low impact, low likelihood. Monitor. Reassess quarterly. Do not overbuild.
This approach helps leaders avoid two common mistakes. The first is underreacting to risks that can interrupt operations. The second is overspending on lower-value concerns that sound urgent but do not materially change business exposure.
Security reporting leaders should demand
Your security update should answer five questions every time. If the report cannot support decisions, it is not executive-ready.
- What changed since the last review.
- What is the top current exposure by business impact.
- What actions closed risk, and what actions slipped.
- Where ownership is unclear or contested.
- What decision leadership must make this week.
Good reporting does not overwhelm leaders with alerts, tool names, or long findings lists. It translates exposure into plain language, shows trend, names owners, and forces action on what matters most.
Executive cadence that drives security readiness
Cadence beats heroics. A routine keeps attention on the basics, catches drift early, and prevents last-minute surprises. Use this operating rhythm as your baseline.
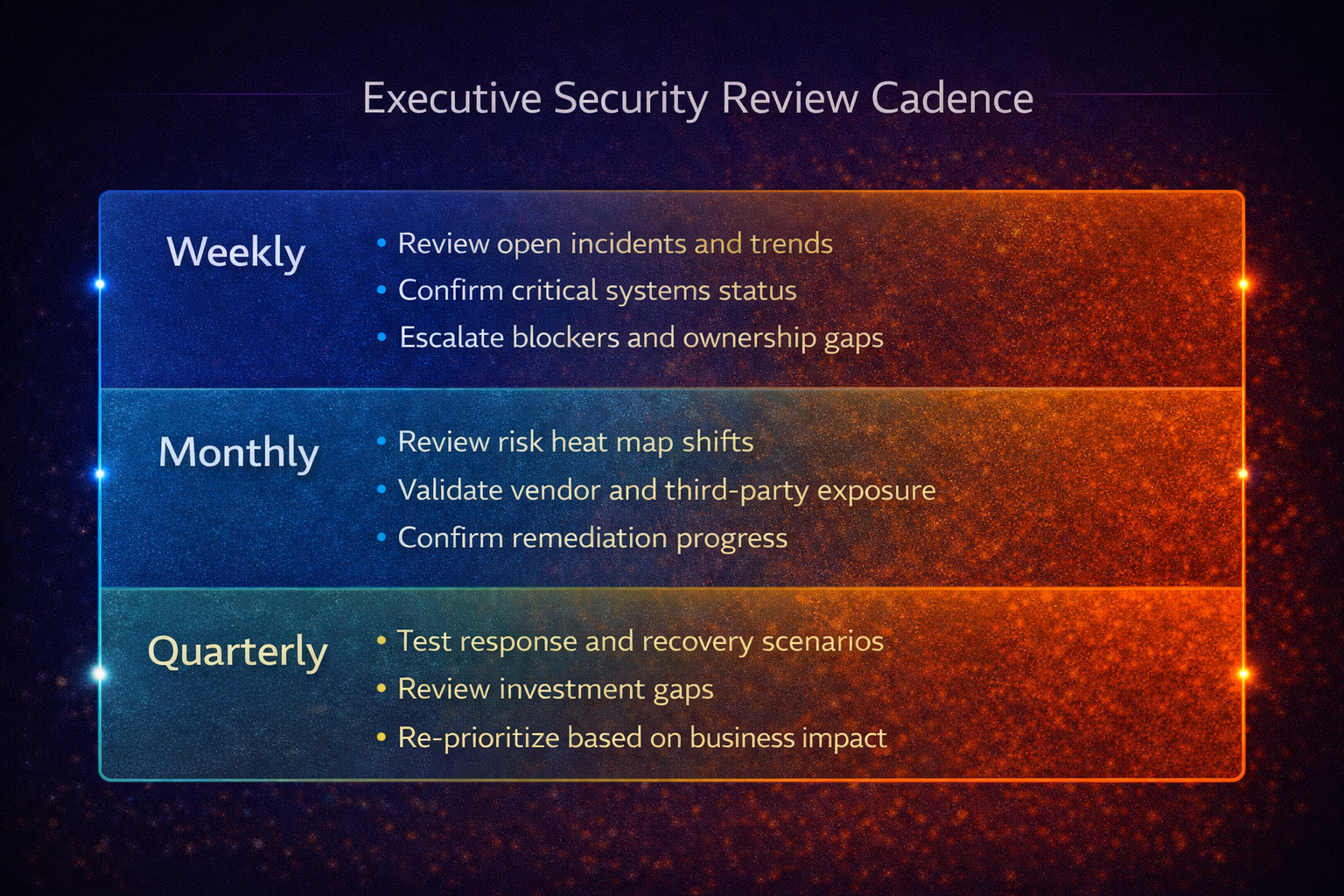
Weekly: triage and follow-through
- Review high-impact risks and overdue actions.
- Confirm incidents and near misses. Capture lessons learned.
- Escalate blockers and remove constraints quickly.
Monthly: controls and vendor review
- Review patching performance, identity health, and monitoring coverage.
- Review vendor exposure, access, incidents, and upcoming renewals.
- Review trend. Are risks decreasing or drifting upward.
Quarterly: resilience and leadership drills
- Run a tabletop exercise with executives and key operators.
- Test recovery for critical systems. Prove restore times.
- Refresh the risk map. Retire stale priorities. Add emerging exposures.
Common readiness gaps and how leaders fix them
Most organizations do not fail because they lack awareness. They fail because basics are inconsistent, ownership is vague, and follow-through is weak. These are common gaps leaders can fix quickly.
Gap: unclear ownership
- Assign an executive owner for each risk category on the risk map.
- Assign an operational owner for each control area.
- Require an action log with due dates and status.
Gap: vendor sprawl and unmanaged access
- Build a vendor register and tier by risk.
- Remove unused access quarterly.
- Put security requirements into contract templates.
Gap: untested recovery
- Run quarterly restore tests and publish results.
- Define recovery objectives for critical systems and fund the gaps.
- Practice manual operations for the most critical business processes.
Gap: reporting that does not lead to decisions
- Require security reporting in business impact language.
- Limit dashboards. Focus on trend, ownership, and actions.
- Escalate decisions that remain open beyond two review cycles.
First 30 days: a practical executive plan
Start with a short baseline. Do not start with tool purchases. Start with visibility, ownership, and routine follow-through.
- Confirm the six-category risk map and name owners.
- Inventory top systems and top data locations. Identify vendor access paths.
- Define a weekly review agenda and start the action log.
- Schedule the first recovery drill and first tabletop exercise.
- Require the next security update in plain business language with clear asks and deadlines.
Quick answers for non-technical leaders
- You do not need deep technical knowledge. You need clear visibility into exposure, ownership, and actions.
- Do not start with more tools. Start with basics, named owners, and review rhythm.
- Do not accept vague reporting. Require business impact, trend, owners, and decisions.
- Do not wait for an incident. Tested recovery and routine reviews reveal gaps before they become crises.
Frequently Asked Questions
What does security readiness mean for non-technical executives?
Security readiness means the organization can prevent common attacks, detect issues quickly, and recover operations with limited business disruption. Executives do not need deep technical detail. They need visibility into risk, clear ownership, and a steady review cadence.
What security areas should executives review regularly?
Executives should review a short risk map across identity and access, data exposure, vendors and SaaS, resilience and recovery, operational discipline, and compliance or audit risk. These categories connect technical controls to business impact.
What should leaders ask in a security review?
Leaders should ask what changed since the last review, what the top current exposure is by business impact, what actions closed risk, what actions slipped, where ownership is unclear, and what decision needs executive attention this week.
How often should executives review security readiness?
A practical cadence is weekly triage for high-impact risks and overdue actions, monthly control and vendor reviews, and quarterly recovery drills and tabletop exercises. Cadence turns security from a fire drill into a routine discipline.
What is the first step to improve security readiness?
Start with visibility and ownership. Confirm the main risk categories, assign executive and operational owners, inventory critical systems and data locations, and begin a short review cadence before buying new tools.
Want security clarity without the jargon
If you receive security updates but still feel uncertain, a focused working session will translate risk into business exposure, establish an executive cadence, and produce a 30-day action plan with owners and measurable outcomes.
Book a consultation